Pack2TheRoot: 12-Year-Old Linux PackageKit Flaw Can Lead to Root Access
Pack2TheRoot is the name of a major new security flaw discovered in a component that is ubiquitous across Linux distributions: PackageKit. This flaw allows users to manipulate package installation and gain "root" privileges. How can you protect yourself? Who is affected? Here’s what you need to know.
Pack2TheRoot: a flaw at the heart of PackageKit
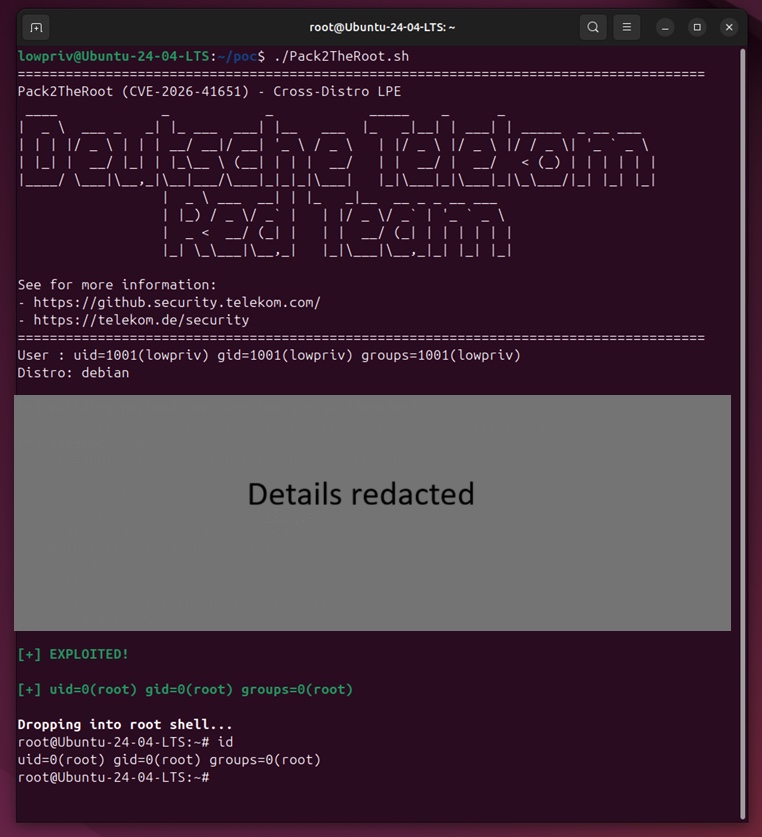
Tracked as CVE-2026-41651 and assigned a CVSS severity score of 8.8 out of 10, the Pack2TheRoot vulnerability was discovered in the PackageKit daemon. As a reminder, this is a service responsible for managing the installation, updating, and removal of software on many Linux distributions.
"PackageKit is a D-Bus abstraction layer that allows the user to manage packages securely through an API compatible with all distributions and architectures.", as stated on the NIST website.
This vulnerability was discovered by Deutsche Telekom’s Red Team and reported to the PackageKit maintainers on April 8, 2026. According to their report, this security issue is related to the way requests tied to certain commands are handled. For example, the pkcon install command can be run without prior authentication in some cases.
As the researchers explain, this discovery was accelerated by the use of AI, especially Claude Opus. "By steering AI-assisted research in a specific direction (using Anthropic’s Claude Opus), we were able to uncover an exploitable vulnerability. This finding was manually reviewed and verified before being responsibly disclosed to the PackageKit maintainers, who confirmed the issue and its exploitability.", we can read.
In practice, this vulnerability could allow an unprivileged attacker to install and remove packages on the local machine. This may enable privilege escalation to root, and thus compromise the Linux machine. At this time, this security flaw is not being exploited, and there is no public PoC (the researchers’ proof of concept has not been published yet).
Which systems are affected?
The Pack2TheRoot vulnerability is present in PackageKit version 1.0.2, first released in November 2014. It affects all versions up to 1.3.4.
As for affected Linux distributions, this includes any distribution that ships with PackageKit integrated and enabled by default. The researchers were also able to test and confirm exploitation on several Linux distributions, including:
- Ubuntu Desktop 18.04 (EOL), 24.04.4 (LTS) and 26.04 (LTS beta)
- Ubuntu Server 22.04 to 24.04 (LTS)
- Debian Desktop Trixie 13.4
- RockyLinux Desktop 10.1
- Fedora 43 (Desktop and Server editions)
This is not an exhaustive list, but it is varied enough to show that this vulnerability affects a large number of Linux machines. To check whether the service is active in the background on your machine (and therefore potentially exploitable), run this command in a Terminal:
systemctl status packagekitTo protect yourself against this security flaw, you must upgrade PackageKit to version 1.3.5.
The researchers also provide the commands to run to display the installed version.
# Debian / Ubuntu
dpkg -l | grep -i packagekit
# Red Hat / Fedora
rpm -qa | grep -i packagekitThe bottom line: this is a striking example of a vulnerability hidden for nearly 12 years and uncovered in part thanks to AI.