RansomLook: The Open-Source Aggregator for Tracking Ransomware Activity
RansomLook is an open-source project that positions itself as a true platform for tracking ransomware activity. It works as an aggregator to monitor ransomware activity, including through cybercriminals' "Data Leak Sites." It is a very interesting resource for security monitoring, especially in the context of Threat Intelligence.
Complete visibility into ransomware activity
Monitoring all ransomware groups is a complex and time-consuming task. In practice, each group, whether it is LockBit, Qilin, Medusa, or even newer players, operates its own portal to publish its victim list. Access is generally provided through the Tor network and a unique address for each portal (known as a Data Leak Site).
In addition, the ransomware ecosystem is volatile: some groups disappear (often after a law enforcement operation), others change their name ("rebranding" operations), or modify the address of their .onion site.
That is where RansomLook comes in by centralizing this information. Based on the RansomWatch project (now archived), RansomLook positions itself as a solution capable of scanning and indexing posts from various data leak sites. The goal: provide continuous visibility into who was hit, by which group, and what data may have been compromised (especially through screenshots shared by cybercriminals).
To date, RansomLook lists more than 30,000 posts from over 500 ransomware groups thanks to tracking carried out since 2022. Beyond data leak sites, RansomLook also monitors other channels such as Telegram.

Beyond offering a simplified interface that avoids having to browse the Dark Web directly to access raw information, here are RansomLook's main features:
- Multi-group indexing: consolidates posts from dozens of ransomware gangs.
- Victim history: ability to browse archives for each group.
- Trends: see which groups are the most active (the ones posting the most messages) over the last X days.
- Intelligence : information on crypto wallets, analyzed files (a section that is still sparse for now), URLs, and even ransom notes is also listed.
- Group profiles : a detailed profile provides more insight into each listed group. It includes several metrics, such as the number of posts, and more specific information, such as the contact email, the URLs associated with the sites used by the group, or the post history.

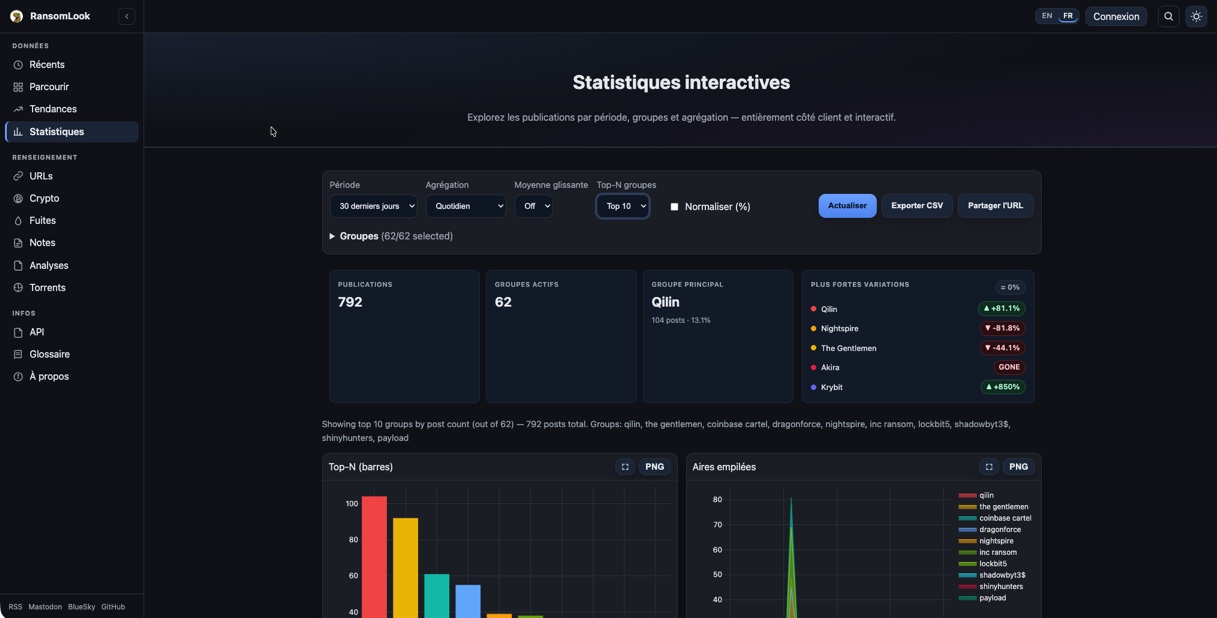
- Statistics: explore posts by time period, groups, and aggregation, which generates charts based on the selected criteria. Data can also be exported in CSV format.
Note : an API is also available to retrieve information about groups, the latest statistics, and observed crypto transactions. This makes it possible to query RansomLook from third-party tools or custom scripts. An RSS feed is also available to follow the global post stream directly.
An asset for Threat Intelligence
RansomLook is useful for Threat Intelligence. By providing a structured data stream, companies, researchers, and people like me can automate part of their monitoring. This makes it possible to collect fresh, up-to-date data every day without doing it manually or building a custom tool to do so.
It is valuable for getting an overview of activity across different groups, whether to track the latest victims or even monitor the emergence of new groups (including through trend tracking). RansomLook's knowledge base also seems interesting for enriching security tools.
From an operational standpoint, thanks to this tool, system administrators, cybersecurity consultants, and security managers (CISOs) can check whether their partners, vendors, and even customers are mentioned on sites where data leaks are disclosed. This type of information can help anticipate spillover risk after an attack on a partner.
RansomLook is an open-source project available on GitHub. Mainly coded in Python, RansomLook relies in particular on data retrieval scripts (scrapers) used to collect fresh data related to each ransomware group. I have not tested it, but you may also want to consider self-hosting your own RansomLook instance.
If you want to discover RansomLook, here are two useful links:









