Proton Pass Security Audit Reveals Fixed Vulnerabilities and Key Findings
Is Proton Pass secure? A new independent audit report provides concrete answers to that question. Spoiler: some vulnerabilities were fixed. Here’s what you need to know.
Table of Contents
A Thorough Assessment Across Proton Pass
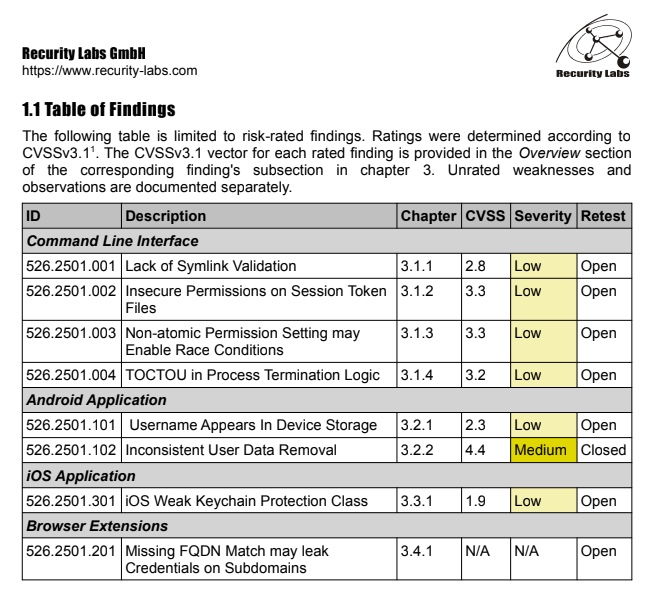
To test the strength of Proton Pass, experts from Recurity Labs (an ISO 270001 certified organization) reviewed nearly every component of the solution. The assessment covered the command-line interface (CLI), the desktop app, the Android and iOS mobile apps, as well as the browser extensions. The backend, meanwhile, was subjected to a "black box" audit, meaning the auditors had no access to the source code or infrastructure.
This audit took place between January and April 2026, and Proton has now made it public (a welcome display of transparency). The first phase of the audit identified 8 security issues in Proton Pass. However, they appear to be minor issues:
- Most of these security issues were associated with low impact.
- Five security flaws were found in the command-line interface (CLI).
- A vulnerability was identified in the iOS app, related to the protection class used for data stored in the Keychain.
- On the Proton Pass browser extensions side, an observation was made about the lack of strict fully qualified domain name (FQDN) matching, which could allow credential autofill across subdomains.
For its part, in its article, Proton highlights two important points:
- No remotely exploitable flaw was detected : users’ vaults cannot be hacked simply by visiting a malicious website or clicking a link.
- No encryption bypass was identified : attackers cannot use shortcuts, backdoors, or keys to bypass the encryption layer.
A Vulnerability Related to Data Deletion on Android
The audit report mentions a medium-severity security flaw in the Android app. Auditors found that when a user signed out of the mobile app and requested data deletion, the operation was only partial.
In practical terms, traces of a previous user’s data could remain on the device in the application’s database files. One file name is specified: db-passkey-wal.
"Since database entries are encrypted, there is no direct risk of password leakage between users, but inconsistencies in user data deletion must nevertheless be fixed.", the report states.
Fixing this vulnerability (and the others) is what Proton’s teams did. Indeed, during the re-audit phase conducted at the end of April 2026, Recurity Labs confirmed that this issue had been corrected. If you want protection against this vulnerability, you must use at least version 1.39.2 of the Proton Pass Android app.
A Memory Management Issue
Let’s finish with the hottest point: a security issue related to how data stored in memory is handled. But before discussing it, note that during the initial assessment, the audit scope was defined as follows: "During the initial assessment, it was established that the application memory was not within the scope of the threat model; observations in this area were therefore not scored. However, the recorded observations were still handled appropriately."
This security issue affects memory handling within the Proton Pass desktop app. Researchers discovered that an attacker with local access to memory could recover the username and master password in clear text, as well as reconstruct obfuscated secrets present in process memory.
This vulnerability stemmed in part from limitations related to string immutability in the sandbox and from the use of a XOR-based obfuscation method deemed unsuitable for sensitive data. Although this type of attack targeting application memory was initially excluded from Proton’s threat model, the vendor made the strong choice to listen to the auditors’ recommendations and revise its position.
And fortunately, Proton took this threat seriously by applying the necessary fix, even though it was outside the initially defined scope.
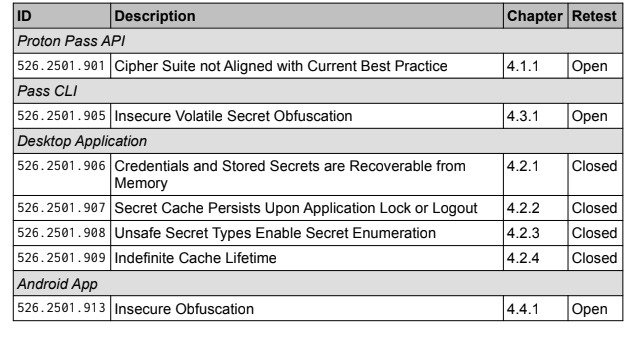
Finally, a note regarding the vulnerability in the iOS app: "As part of the new round of iOS app tests, Recurity Labs was informed that a fix for the only vulnerability found, related to the use of weak protection classes, had been developed, but it would not be deployed because it was a high-risk change, and the iOS version had to be excluded from the new test round."
Finally, despite the detection of several issues during the audit, Recurity Labs considers Proton Pass’s overall security posture to be "well above average". The good news is that Proton takes the security of its applications seriously, as shown by its strong responsiveness in patching the reported vulnerabilities.
You can read the audit report here.