Wazuh Issues Patch for Critical CVE-2026-30893 Flaw
A critical security flaw, tracked as CVE-2026-30893 and rated CVSS 9.9, has recently been disclosed in Wazuh. What are the risks? How can you protect yourself? Here’s what you need to know.
What We Know About CVE-2026-30893
The open source Wazuh platform is affected by a critical security flaw: CVE-2026-30893. This path traversal vulnerability is located in the extraction routine used for cluster synchronization. In practice, it allows a cluster peer (which must be authenticated) to write arbitrary files on other cluster nodes. The write occurs outside the extraction directory originally intended by the system.
"This flaw can lead to code execution in the context of the Wazuh service by overwriting Python modules loaded by Wazuh components (PoC available in a separate attachment).", states the security advisory dated April 29, 2026. If the service associated with the cluster runs with elevated privileges, this vulnerability can allow the host to be compromised.
This vulnerability affects Wazuh servers from version 4.4.0 up to versions earlier than 4.14.4. In other words, Wazuh Server update 4.14.4 fixes this security issue (or any newer version).
France Ranks Among the Most Exposed Instances
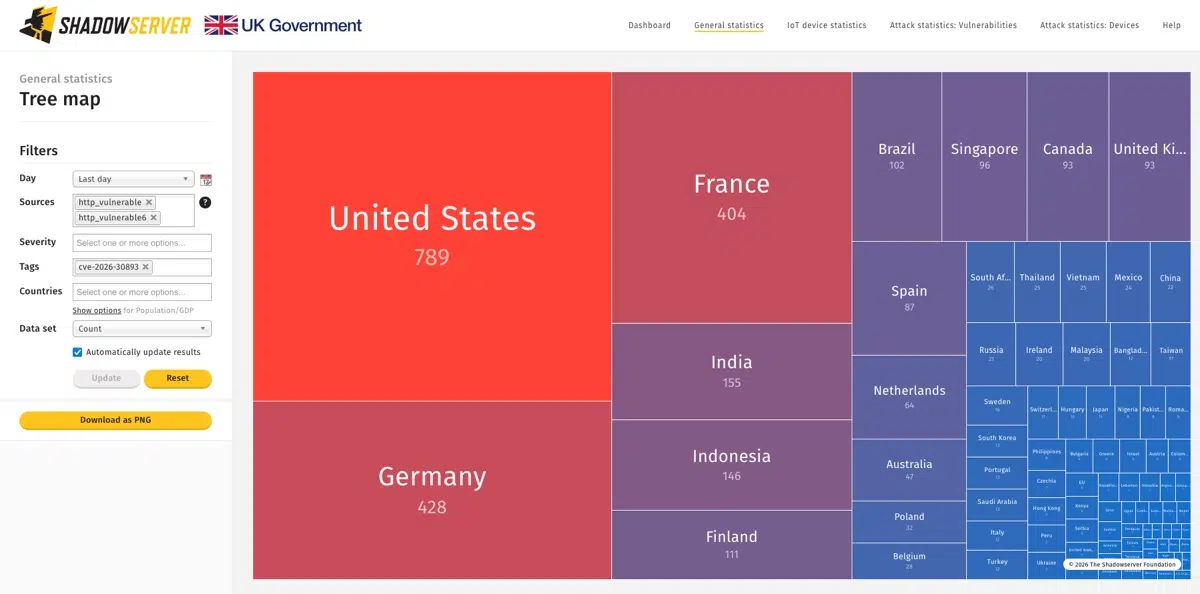
According to statistics collected by the Shadowserver Foundation and applying a specific filter for this vulnerability, many exposed instances appear to be vulnerable to this security flaw. However, as you now know, exploitation is only possible in a specific context. Nodes that are not members of a cluster, or those where cluster mode is disabled, are not vulnerable even if they are not up to date.
Here are the top 3 countries with the highest number of Wazuh servers potentially vulnerable to CVE-2026-30893:
- United States : 789 instances
- Germany : 428 instances
- France : 404 instances
In total, as of May 12, 2026, the Shadowserver Foundation counts around 3,500 IP addresses associated with potentially vulnerable Wazuh servers.