DigiCert Breach: Stolen Certificates Used to Sign Malware
A cybercriminal managed to break into DigiCert's internal systems, the digital certificate giant, and steal data used to issue EV code signing certificates. The goal: sign malware to make it look legitimate. Here's what we know about this security incident.
Customer Support as the Entry Point
The incident, detailed in a report published by DigiCert, began on April 2, 2026. The attack method relied on a classic technique that still causes plenty of damage: social engineering. By posing as a customer to technical support, an attacker repeatedly sent a booby-trapped ZIP archive while claiming they wanted to share a screenshot with support.
Inside the archive was actually a .scr file (a Windows screensaver). A DigiCert technician managed to execute this file on their workstation, even though it had been blocked several times by security tools (which should have raised an alert). The next day, on April 3, 2026, DigiCert teams were able to stop the malicious process.
Unfortunately, a second machine was infected by the same malicious file. On that machine, the CrowdStrike EDR agent was misconfigured: alerts were not forwarded to the centralized management console. This was not without consequences, since the malware remained active on that machine for two weeks.
Stolen and Exploited Initialization Codes
The attacker used the compromised support account to access DigiCert's internal customer support portal. This portal includes a feature that allows analysts to view customer accounts to facilitate troubleshooting (a sort of "log in as"). The problem is that this feature exposed "initialization codes" linked to pending EV code signing certificate orders.
Possession of such a code, acting like a one-time identifier, combined with an already approved certificate request, is enough to generate and retrieve a valid EV certificate. By collecting this data across several customer accounts, the attacker was able to get their hands on a set of certificates.
"Our subsequent investigation revealed that the attacker had managed to obtain initialization codes for a limited number of code signing certificates, only a very small number of which were then used to sign malware," DigiCert said.
Here are some figures shared by DigiCert:
- 60 certificates issued during the exposure period were revoked as a security measure.
- 27 certificates were directly linked to the attacker's activity.
- 11 of them had already been reported by security researchers as being used in malicious campaigns (and 16 others were identified through DigiCert's internal investigation).
These valuable certificates were used to sign Zhong Stealer malware payloads, a threat known for stealing credentials and cryptocurrency. According to this analyst, the Chinese cybercriminal group GoldenEyeDog is believed to be behind the intrusion at DigiCert. As explained there and as shown in the image below, these fraudulent EV certificates were issued in the names of well-known companies, including Lenovo and Kingston.
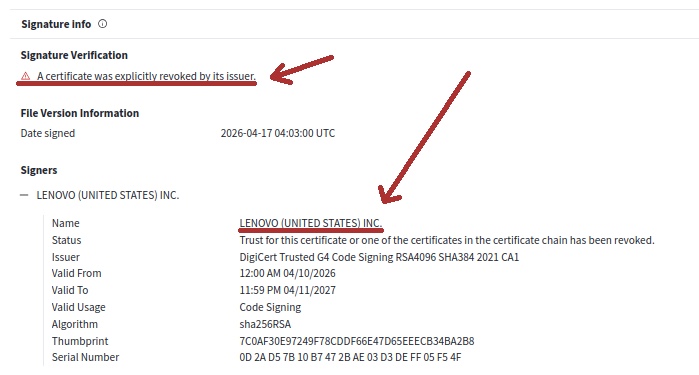
DigiCert says there were no other malicious actions beyond the use of validation codes to obtain code signing certificates. Fortunately, these certificates have now been revoked. They represented a real threat because they make it possible to sign a malicious executable and present it with a valid signature to the operating system (DigiCert being a trusted certificate authority).
The detailed report on this incident is available on this page.









