NGINX Rift CVE-2026-42945: A 18-Year-Old Critical Flaw Threatening Web Servers
NGINX Rift is the name of the new critical vulnerability discovered in NGINX Plus and NGINX Open Source. Present in the codebase for 18 years, this flaw allows an unauthenticated attacker to execute remote code or crash the NGINX server using web requests.
Table of Contents
NGINX Rift: an 18-year-old flaw
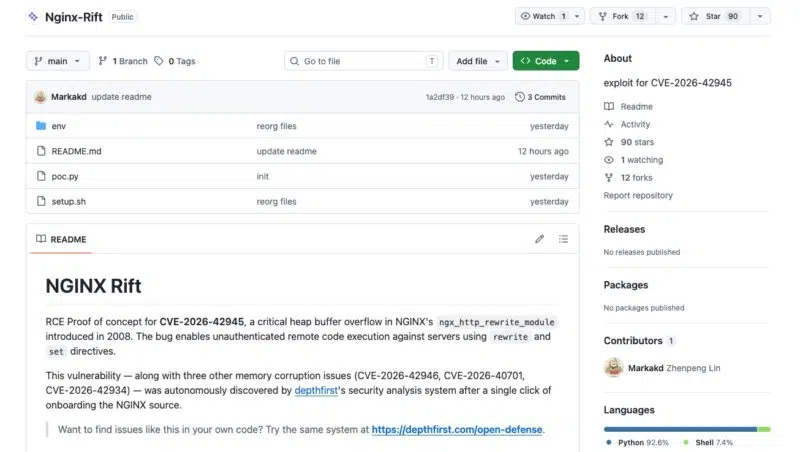
Discovered by cybersecurity researchers at depthfirst, this vulnerability nicknamed NGINX Rift is tracked as CVE-2026-42945 and carries a severe CVSS v4 score of 9.2 out of 10. It is therefore considered critical. This heap buffer overflow affects the ngx_http_rewrite_module module in NGINX. It is thus tied to NGINX URL rewriting mechanisms.
"We used the depthfirst system to analyze the NGINX source code, and it autonomously detected four remote memory corruption flaws, including a critical heap buffer overflow that appeared in 2008.", notes the report.
The researchers explain that this flaw comes from an is_args flag that is not properly propagated during a sequence of rewrite and set directives, resulting in the allocation of a too-small memory buffer. During the copy phase, attacker-controlled escaped URI data is then written beyond the bounds of this buffer, causing an overflow that enables remote code execution.
Remote code execution is possible on systems where ASLR is disabled (a memory protection mechanism). In addition, repeated requests can trigger a denial of service for all websites hosted by the instance.
What is concerning is that there is no need to be authenticated, or even to have any session at all. The only requirement is being able to reach a vulnerable NGINX Web server over HTTP in order to send it a specially crafted request designed to exploit this flaw.
A PoC exploit has been published on GitHub by the depthfirst researchers.
Three other vulnerabilities patched in parallel
In addition to the NGINX Rift flaw, responsibly disclosed on April 18, 2026 by depthfirst, F5 also fixed three other security issues in NGINX:
- CVE-2026-42946 (CVSS 8.3): excessive memory allocation in the
ngx_http_scgi_moduleandngx_http_uwsgi_modulemodules. An unauthenticated remote attacker positioned as a man-in-the-middle could read NGINX worker process memory or restart it. - CVE-2026-40701 (CVSS 6.3): a Use-After-Free flaw in the
ngx_http_ssl_modulemodule, allowing limited data modification or process restart when client verification and OCSP are enabled. - CVE-2026-42934 (CVSS 6.3): an out-of-bounds read in
ngx_http_charset_module, which could lead to memory disclosure or an NGINX process restart.
How to protect and patch your servers
To protect against these multiple flaws, applying the latest patches is the only truly adequate line of defense. A very large number of versions are affected. Here is a summary of what was reported by F5, the publisher of NGINX, in the security advisory.
| Affected product | Affected versions | Fixes |
| NGINX Plus | R32 - R36 | 37.0.0, R36 P4, R32 P6 |
| NGINX Open Source | 1.0.0 - 1.30.0 0.6.27 - 0.9.7 | 1.31.0 1.30.1 |
| NGINX Instance Manager | 2.16.0 - 2.21.1 | None |
| F5 WAF for NGINX | 5.9.0 - 5.12.1 | None |
| NGINX App Protect WAF | 5.1.0 - 5.8.0 4.9.0 - 4.16.0 | None |
| F5 DoS for NGINX | 4.8.0 | None |
| NGINX App Protect DoS | 4.3.0 - 4.7.0 | None |
| NGINX Gateway Fabric | 2.0.0 - 2.5.1 1.3.0 - 1.6.2 | None |
| NGINX Ingress Controller | 5.0.0 - 5.4.1 4.0.0 - 4.0.1 3.5.0 - 3.7.2 | None |
Note that for the very old NGINX Open Source 0.6.27 - 0.9.7 branch, no patch is planned. You must move to a newer version, as indicated in the table.
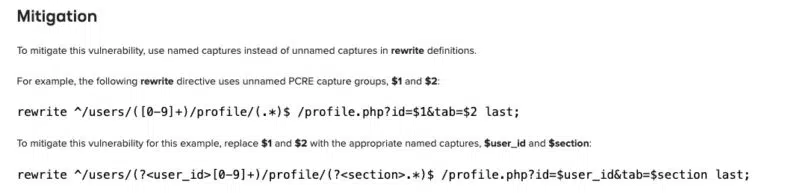
If deploying the patch for CVE-2026-42945 immediately is not possible on your server right now, be aware that a workaround exists. In its security advisory, F5 recommends modifying your rewrite rules by systematically replacing unnamed captures with named captures within each affected directive. You will find an example below.