Linux: Forgotten Kernel Flaw Lets Attackers Steal SSH Keys and Read Root Files
After Copy Fail, Dirty Frag, and Fragnesia, it’s not over yet! Security researchers at Qualys have just revealed a new vulnerability that offers privilege escalation on a silver platter. Here’s what you need to know about this flaw in the Linux kernel.
A vulnerability identified 6 years ago
The bad streak of Linux vulnerabilities continues. But first, an important clarification: Jann Horn, a member of the Google Project Zero team, had already identified this security flaw in 2020. At the time, a patch was even proposed, but curiously it was never merged into the main codebase. One might think it was simply not the right season.
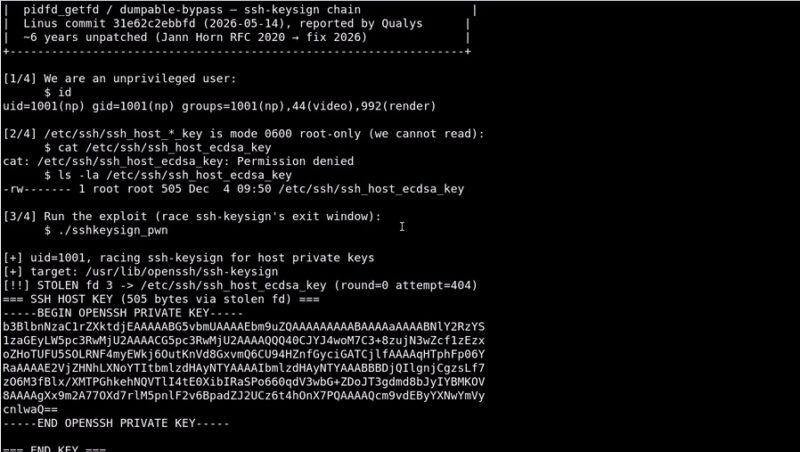
Over the past few hours, this flaw has started making headlines again, and this time it will be fixed. And for good reason: it is a serious critical flaw. It allows a non-privileged local user to read any file on the system, including files owned by root. As a result, it is possible to read files such as /etc/shadow and even the SSH keys available on the Linux system.
In practice, this privilege escalation is not as straightforward as in the case of CopyFail; however, its impact is still very real. Indeed, this attack technique relies on exploiting a race condition within the system.
As Alexis Koestel explained in his LinkedIn post (by the way: thank you for flagging this flaw to me):
- When a process ends, it frees its memory but keeps its open files for a very short time.
- A simple legitimate system call is then enough to recover those accesses before they disappear permanently.
It is also possible to test the exploitation of this vulnerability yourself, since an exploit named ssh-keysign-pwn has been published on GitHub. It relies in particular on the __ptrace_may_access() function in the Linux kernel. This PoC includes two files: one to display the contents of SSH keys (located under /etc/ssh) and another to display the contents of the /etc/shadow file.
As a reminder, the /etc/shadow file is a critical Linux system file, restricted to the root user, which securely stores the hash of user account passwords (as well as parameters related to those accounts).
A new universal exploit... and a patch coming soon
This new vulnerability is also a universal exploit, like those discovered in recent days. That means it can be exploited across different Linux distributions, including Ubuntu, Debian, CentOS, and Arch Linux.
Fixes are expected in the next few hours or days, depending on how quickly maintainers respond. Linus Torvalds, meanwhile, has already pushed the fix into the Linux kernel source code via a new commit intended to be included in a future release. In the meantime, all current versions of the Linux kernel are vulnerable...








