Did Claude Mythos Really Discover a New FreeBSD Root-Full Vulnerability?
In early April 2026, Anthropic claimed that its Claude Mythos model was the first AI to identify a security flaw granting root access on FreeBSD (CVE-2026-4747). However, a new report published by Rival Security points to a recycled vulnerability.
A "new" flaw that looks familiar
The vulnerability discovered by Claude Mythos and documented under CVE-2026-4747 concerns a remote code execution (RCE) issue in the NFS server and the RPCSEC_GSS authentication module via Kerberos, natively integrated into FreeBSD (within its kernel).
This security flaw is a classic buffer overflow tied to the svc_rpc_gss_validate() function, where an RPC header is rebuilt in a 128-byte buffer. The code first writes 32 bytes of header, then copies the entire credentials body into the remaining space (96 bytes), with no bounds checking at all. If the size exceeds that space, the stack overflows.
But the origin of this code is much older. It goes back to Sun Microsystems' ONC RPC and NFS protocols, created in 1984. Much of the open-source code implementing these functions was developed in the 1990s by the CITI (Center for Information Technology Integration) at the University of Michigan. FreeBSD maintains its base system in a single repository, and the vulnerable code was copied there several years ago.
The ghost of CVE-2007-3999
Since this code has been widely shared and copied, notably in the MIT Kerberos implementation, did the AI really discover a new flaw? The Rival Security report presents another version of the story. While digging through the archives, the researchers found another security flaw: CVE-2007-3999.
Its NIST description mentions a stack-based buffer overflow in the svcauth_gss_validate function in MIT Kerberos, allowing arbitrary code execution. Sound familiar? I think so...
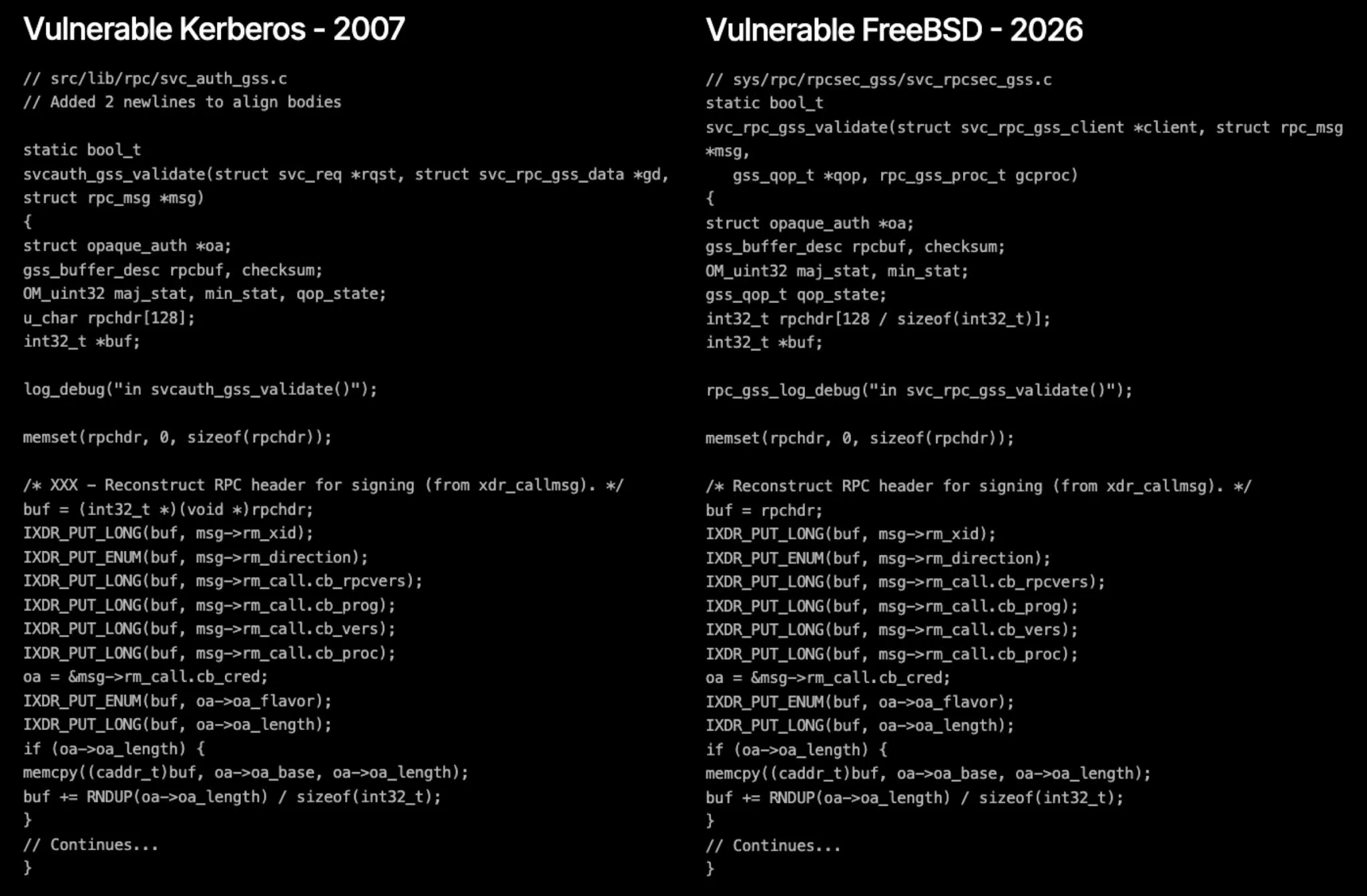
In reality, if you compare the vulnerable Kerberos code (patched in 2007) with the code present in the FreeBSD source tree discovered by Mythos in 2026, the resemblance is striking. The two functions are practically identical at the code level. The logic is the same, even though the functions have different names and the accepted arguments are not identical in both cases. Moreover, the patch applied to fix FreeBSD is almost a copy-paste of the 2007 fix.
As a result, the researchers believe that Claude Mythos identified and exploited a vulnerability whose traces were very likely already present in the large training dataset it used. Here are the vulnerable code snippets as presented in the Rival Security report.
Ultimately, this perspective is interesting and highlights the risks associated with recycled code. This is especially true because LLMs are likely to "regurgitate" the same insecure patterns they were trained on. On the other hand, LLMs also help identify them, which makes AI a powerful scanner (including for what is known as pattern matching).