Critical vm2 Sandbox Escape Flaw Exposes Node.js Applications
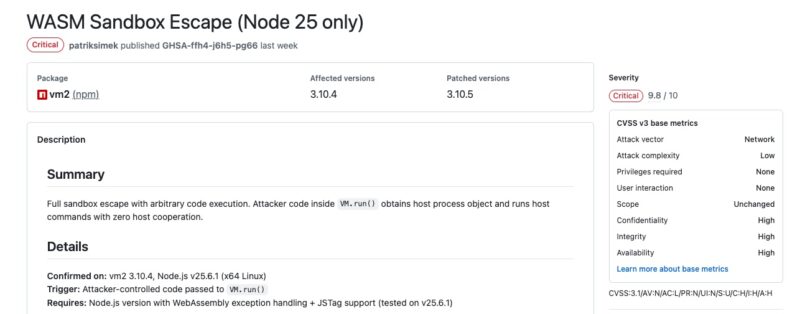
A new alert in the Node.js ecosystem: a critical security flaw has been discovered in the vm2 library, which is widely used by sandboxing mechanisms. Here’s the key information you need to know about this vulnerability tracked as CVE-2026-26956.
A Sandbox Escape
With more than 1.3 million weekly downloads on NPM, the open-source vm2 library is among the most popular. The purpose of this library is to allow unapproved JavaScript code (for example, suspicious code) to run in an isolated environment (sandbox). As a result, it is used by Node.js projects and SaaS applications.
The root cause of this flaw lies in improper handling of exceptions that move between the isolated environment and the host. Normally, vm2 relies on JavaScript-level protections to block errors coming from the host and secure communication.
Exploiting this vulnerability unfolds in several steps:
- The attacker triggers a specially crafted
TypeErrorusing a "Symbol-to-string" conversion. - This causes a host-side error object to leak directly into the sandbox, without
vm2sanitizing it. - Since this object comes from the host environment, the attacker can regain access to internal Node.js components (such as the
processobject). - The attacker can ultimately execute commands of their choice on the victim’s system.
As you can see, this vulnerability makes it possible to escape the sandbox and execute code on the host.
However, there are technical prerequisites for exploitation to work. As noted in the security advisory published by the maintainer, only Node.js 25 environments with WebAssembly exception handling and JSTag support enabled are affected. That same security bulletin also includes a proof of concept (PoC).
How Can You Protect Yourself from CVE-2026-26956?
The CVE-2026-26956 flaw affects, at a minimum, version 3.10.4 of vm2 (older versions may also be affected). So, ideally, to protect your application:
- Upgrade your
vm2library to version 3.10.5 or later. - Upgrade to the latest branch of the library, which is currently 3.11.2.
Finally, this is not the first time that a critical flaw in vm2 has made it possible to escape the sandbox. It brings to mind a series of vulnerabilities patched in April 2023 in this same library.








