Palo Alto Networks Warns of a New Zero-Day Already Being Exploited (CVE-2026-0300)
A new security alert from Palo Alto Networks: a zero-day vulnerability (CVE-2026-0300) that can be exploited without authentication and is already being used by cybercriminals affects the User-ID authentication portal in PAN-OS. Here’s how to protect yourself.
Remote code execution without authentication
On May 6, 2026, Palo Alto Networks published a security bulletin about CVE-2026-0300, a buffer overflow vulnerability with a CVSS v4 score of 9.3 out of 10. This new flaw affects firewalls running on hardware appliances (PA-Series) and virtual appliances (VM-Series) running the PAN-OS operating system. As Palo Alto Networks explains in its security bulletin, this vulnerability is located in the User-ID authentication portal, also known as the captive portal.
The severity of this vulnerability comes from the way it is exploited: a remote, unauthenticated attacker can send specially crafted network packets to a vulnerable device with the portal enabled. This allows arbitrary code to be executed with "root" privileges, without requiring any user interaction.
Palo Alto Networks also confirmed that this vulnerability has been exploited by cybercriminals, without specifying the nature of the attacks observed. "We have observed limited exploitation targeting Palo Alto Networks User-ID™ authentication portals exposed to untrusted IP addresses and/or the public Internet.", it states.
To give an idea of the potential attack surface, a report published by Rapid7 indicates that the Shodan search engine lists around 225,000 PAN-OS instances exposed on the web. According to The ShadowServer service, there would be about 5,800 Palo Alto Networks instances accessible from the Internet, which is not quite the same thing. But be careful: this feature is not necessarily enabled.
How can you protect yourself from CVE-2026-0300?
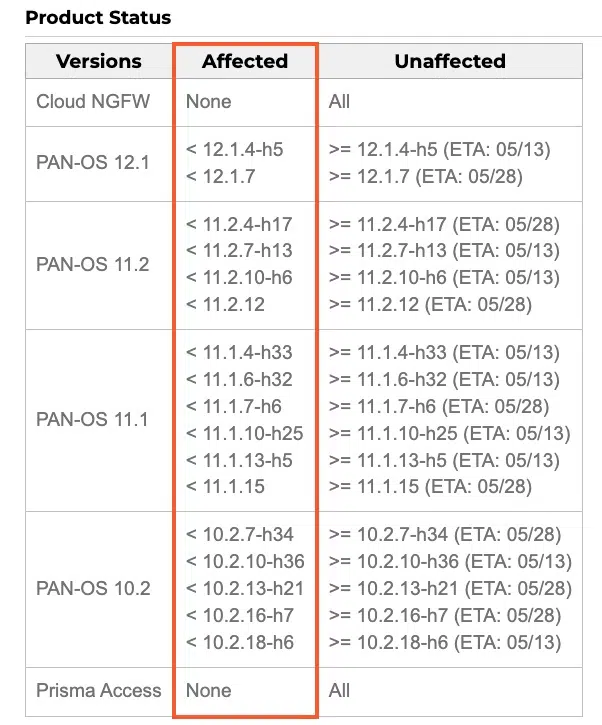
At the moment, Palo Alto Networks does not provide any official patch! They are currently being prepared, and the first fixed versions (for the PAN-OS 10.2, 11.1, 11.2, and 12.1 branches) will begin on May 13, 2026, and continue through May 28, 2026.
Here is the list of affected versions and the expected patches (with dates).
In this context, all organizations using this authentication portal are advised to apply one of the following mitigation measures while waiting for patches to become available:
- Restrict access: limit access to the User-ID authentication portal to your trusted internal zones only.
- Disable the feature: if this portal is not essential, or if you can do without it temporarily, disable it.
Finally, note that Prisma Access, Cloud NGFW, and Panorama are not affected by this flaw.