cPanel Servers Hit by Sorry Ransomware After Critical Linux Flaw
The critical security flaw affecting cPanel and WHM, tracked as CVE-2026-41940, is currently being massively exploited. Through it, attackers can take control of Linux servers and then encrypt data with the Sorry ransomware. Here’s what we know.
A critical security flaw: CVE-2026-41940
The Linux-based web hosting control panel cPanel, as well as its WHM server management interface, are directly targeted by a large-scale attack campaign. This campaign is directly tied to a critical security flaw (CVE-2026-41940) patched a few days ago and allowing authentication bypass.
This flaw is also believed to have been exploited as a zero-day since the end of February. But since this vulnerability was disclosed, the situation has worsened: hundreds of hacked websites are being indexed on Google. Among the ongoing campaigns, one involves the use of the Sorry ransomware to encrypt data.
The Sorry ransomware encrypts Linux servers
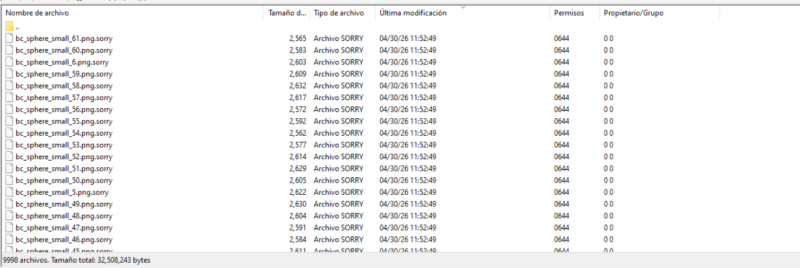
Once access to the server has been obtained through the cPanel flaw, attackers deploy the Sorry ransomware. Written in Go and designed to target Linux servers, this ransomware encrypts files and adds the .sorry extension to each encrypted file. As often happens, a ransom note (README.md) is dropped on the server and, without the encryption key, data recovery is impossible.
In recent days, various posts on this topic have been published on the web, such as on the Kaspersky forum, for example. "My Linux server was recently infected with ransomware that changed the extension of all the files on my website to .sorry.", we can read.
What surprised me was a post published by The Shadowserver on X. It reveals that cPanel servers previously compromised via the CVE-2026-41940 flaw are being exploited by cybercriminals to carry out other malicious actions. In practical terms, these hijacked servers have been observed:
- Launching automated brute-force attacks.
- Scanning the web for new vulnerable targets.
- Launching exploits against other infrastructures.
The Shadowserver message specifies that as of April 30, 2026, at least 44,000 IP addresses running cPanel had already been compromised by these ongoing attacks. The trend appears to be downward if we refer to the updated statistics.
In short, the CVE-2026-41940 security flaw must be taken very seriously: if you use cPanel or WHM, you need to patch your server immediately. This is even more important if the management interface is exposed to the web, which is unfortunately very common with this type of tool.









