Copy Fail: Critical Linux Flaw Lets Attackers Gain Root Access
Copy Fail is the name of a new critical security flaw discovered in Linux that can be used to gain root access on the vast majority of Linux distributions released since 2017. That’s right. Here’s the key information you need to know about this vulnerability.
Copy Fail: Overview of CVE-2026-31431
The new Copy Fail security flaw, tracked as CVE-2026-31431, is a logic bug in the Linux kernel. It was introduced in 2017, when a developer added an optimization to a file named algif_aead.c. The problem is that a simple 732-byte exploit written in Python can be used to gain root access on Linux.
This security flaw, which was discovered with the help of AI using the Xint Code tool, enables local privilege escalation. It affects the Linux kernel cryptographic subsystem, specifically authencesn. By combining the AF_ALG API and the splice() function, an unprivileged attacker can exploit this vulnerability. The result: they can write 4 bytes of data directly into the page cache of any file present on the system, including /usr/bin/su. That is enough to launch a Terminal as root and gain access.
Here, we are dealing with a critical vulnerability that is easy to exploit, especially compared with other security flaws. The researchers also note that the exploit works every time: "This script works exactly the same way on all distributions and architectures tested, including Ubuntu, Amazon Linux, RHEL and SUSE. No distribution-specific offsets. No recompilation. No version checks in the exploit."
The exploit code (PoC) mentioned above is just a simple Python script using standard Python libraries (os, socket and zlib modules). In other words, there are no external dependencies.
How can you protect yourself from the Copy Fail flaw?
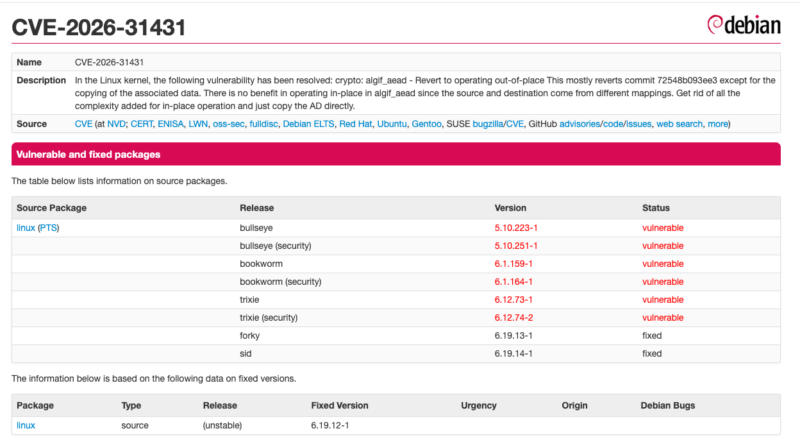
The report published by the researchers provides a few more specific names of tested distributions: Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 10.1, and SUSE 16. In reality, many distributions and versions are affected. For example, on the Debian side, there is still no security fix at the time I am writing this article (see this page).
This flaw threatens a large number of machines (personal computers, VPSs, shared servers, and more). To protect yourself, you should monitor the release of security patches from the maintainers of the various Linux distributions. The patch consists of reverting the optimization introduced in 2017, which removes the flaw as a result (the commit in the Linux kernel already exists).
In the meantime, an effective mitigation is to disable the algif_aead module at the Linux kernel level using the following commands:
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.conf
rmmod algif_aead 2>/dev/null || trueI have not tested this workaround, but from what I have read, it should not really affect most systems. For example, it does not impact the LUKS disk encryption mechanism.