Credential Theft on Windows: Microsoft Confirms CVE-2026-32202 Is Being Exploited
Microsoft has updated its security bulletin for CVE-2026-32202 to indicate that this vulnerability is being exploited. Here's what you need to know about this security flaw affecting both Windows and Windows Server.
CVE-2026-32202: a flaw in Windows Shell
Disclosed on April 14, 2026, alongside this month's Patch Tuesday, this vulnerability associated with the CVE-2026-32202 reference is located in the Windows Shell interface. This is a core component of Windows, especially for managing access to objects (see this page).
This spoofing vulnerability is described by Microsoft as follows: "An attacker who successfully exploited this vulnerability could view some sensitive information, but not all resources in the affected component would necessarily be disclosed to the attacker. The attacker cannot modify the disclosed information or restrict access to the resource."
This means an attacker could gain access to sensitive information without being able to modify it. Exploitation relies on a malicious file sent to a user, which the user would then execute on their machine.
So far, this vulnerability has not drawn much attention. However, on April 27, 2026, Microsoft revised the page associated with this update to indicate that it was being exploited by cybercriminals. The company did not provide any further details on the matter.
The shadow of the APT28 group...
While doing some research on this CVE, I came across a report published by Akamai and written by Maor Dahan. According to him, this vulnerability is the result of an incomplete patch deployed to fix a previous security flaw: CVE-2026-21510 (CVSS 8.8/10), patched by Microsoft in February 2026.
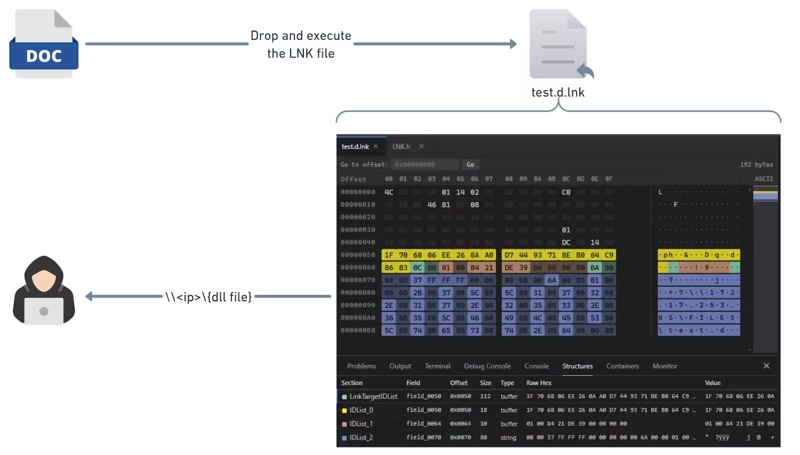
More importantly, it is said to have been exploited by a state-linked Russian group: APT28, also known by other names, including Fancy Bear. During a campaign conducted in December 2025 targeting Ukraine and several European Union countries, these hackers used malicious Windows shortcut files.
The Akamai researcher details this attack method: "APT28 exploits the Windows Shell namespace parsing mechanism to load a dynamic-link library (DLL) from a remote server using a UNC path. The DLL is loaded as part of Control Panel objects (CPL) without proper validation of the network zone." - This last sentence refers to the zone identifier that is ignored (the Zone.Identifier field).
The patch integrated in February 2026 reduces the risk of remote code execution (RCE) by forcing a SmartScreen check, which had previously been bypassed. However, it still allowed the victim's machine to authenticate to the attacker-controlled server without any user interaction.
This technique relies on the use of an SMB connection initiated toward the attacker's server. At that point, an authentication attempt via the NTLM protocol is also triggered, and that opens the door to credential theft.
"This SMB (Server Message Block) connection triggers an automatic NTLM authentication process, sending the victim's Net-NTLMv2 hash to the attacker, who can then use it to carry out NTLM relay attacks and offline attacks to crack the password," the researcher explains.
Ultimately, the vulnerability appears to have been exploited at least by the APT28 group. If you want to protect yourself against this threat, you need to install the April 2026 updates on your Windows 10, Windows 11, and Windows Server systems (2012 through 2025).









