Bitwarden CLI Supply Chain Hack: Malicious Version Spread via NPM
Bitwarden CLI, the tool developed by the creators of the Bitwarden password manager, was targeted in a cyberattack. Attackers managed to publish an infected version designed to steal sensitive information from victims' machines.
A Compromise Through the CI/CD Pipeline
A new report published by Socket researchers describes the compromise of Bitwarden CLI in the wake of the attack that targeted Checkmarx. Over the past several weeks, supply chain cyberattacks via GitHub Action have kept piling up (we also remember Axios).
Note : this package gets around 250,000 downloads per month on NPM. It allows users to access and manage a Bitwarden password vault from the command line.
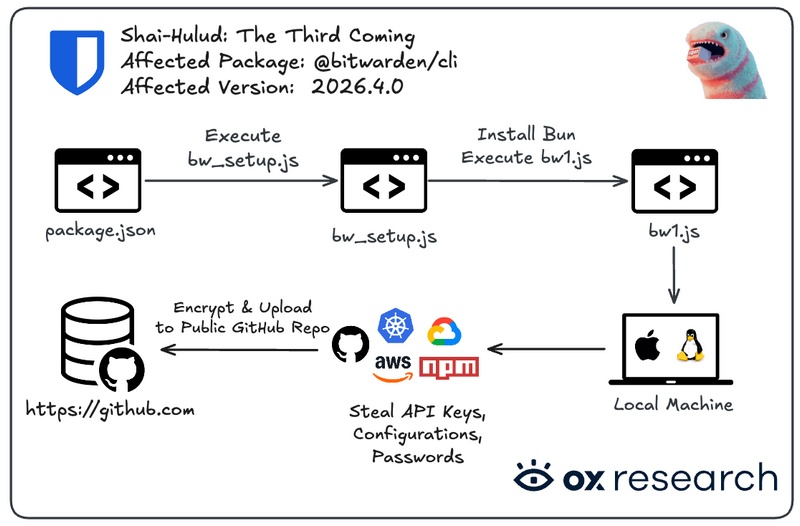
The compromised version appears to be package @bitwarden/cli@2026.4.0, with malicious code hidden inside a file named bw1.js. Fortunately, this version is no longer available online.
To pull off the attack, the threat actors compromised a GitHub Action directly inside Bitwarden's CI/CD pipeline. They abused stolen GitHub tokens, injected a new workflow capable of capturing secrets, and then pushed the malicious release to users.
This infected Bitwarden CLI version was designed to steal sensitive information and exfiltrate it so it would end up in the attackers' hands. The targeted data included the following:
- GitHub and npm tokens
- SSH keys (
.ssh) - Environment files (
.env) - Command history
- Secrets associated with GitHub Actions and Cloud environments
- Claude and MCP configuration files
- NPM configuration files (
.npmrc)
It is worth noting that the infrastructure used by the attackers (the C2 server) is the same as the one defined in the mcpAddon.js file tied to the Checkmarx compromise. As a result, it is highly likely that the TeamPCP group is once again behind this cyberattack.
"Exfiltration also occurs via the GitHub API (commit-based) and the npm registry (token theft/republication).", the researchers explain.
A separate report published by OX Security warns about the growing number of these attacks: "Shai-Hulud is one of many supply chain attacks that took place in 2026, and this trend does not seem likely to slow down anytime soon, with cybercriminals stockpiling more and more credentials and compromising an increasing number of developers."
Indeed, OX Security spotted the string "Shai-Hulud: The Third Coming" in the compromised package, suggesting this is one stage in the ongoing compromise campaign...
Bitwarden's Response
When contacted by The Hacker News, Bitwarden confirmed the compromise while reassuring users: vault data was never compromised. The malicious package was only available on NPM for a short window on April 22, 2026, between 5:57 p.m. and 7:30 p.m. Eastern Time.
Bitwarden stated: "The investigation found no evidence that end-user vault data was accessed or put at risk, nor that production data or production systems were compromised." - However, be careful if you use Bitwarden CLI and downloaded the infected version.
As soon as the anomaly was detected, the compromised access was revoked, the malicious version was removed from npm, and remediation measures were launched. Finally, a CVE identifier will soon be assigned to describe the vulnerability associated with version 2026.4.0. On NPM, the current safe version remains 2026.3.0.









