Dirty Frag Zero-Day Gives Attackers Root Access on Linux
Dirty Frag is the name of a new critical security flaw affecting Linux machines. This zero-day vulnerability is similar to Copy Fail because it enables privilege escalation to root. Here’s the essential information you need to know about this potential threat.
Table of Contents
Dirty Frag: it blew up before the planned date
The Dirty Frag vulnerability was discovered by researcher Hyunwoo Kim, who had initially planned a coordinated disclosure for May 12, 2026. However, someone managed to uncover information related to this vulnerability, and so everything was published early this Thursday, May 7, 2026.
Hyunwoo Kim decided to publish all the details, especially to alert the community: "Because the embargo was broken, no patch or CVE exists for these vulnerabilities. After consultation with the maintainers of linux-distros@vs.openwall.org, and at the maintainers' request, I am publicly releasing this Dirty Frag document.".
As of now, here is what is available:
- A full technical write-up presenting this vulnerability in full detail,
- A "universal" exploit code since it works across many Linux distributions.
This is reminiscent of the situation with CopyFail. Except that here, it is a different vulnerability: Dirty Frag. For now, there is no CVE reference, and above all, no patches yet (even if that is starting to change).
What is the Dirty Frag vulnerability?
There are similarities between Dirty Frag and two other security flaws: CopyFail (2026) and Dirty Pipe (2022). This new exploit actually relies on two vulnerabilities, one in xfrm-ESP and the other in RxRPC. In both cases, it is a security issue related to writing data into the page cache (as with CopyFail). In fact, the researcher explains that the CopyFail flaw motivated him to carry out this research work.
The vulnerability is triggered when the Linux kernel performs cryptographic operations "in place". This logic flaw makes it possible to overwrite data directly in RAM. As a result, an unprivileged user can modify on the fly the content of critical operating system files that are normally read-only, such as /usr/bin/su or /etc/passwd.
If the researcher chained two vulnerabilities, that is no coincidence. It was necessary to create a universal exploit, meaning an exploit capable of bypassing the specific defenses of certain systems (AppArmor, for example).
- The xfrm-ESP vector: this vulnerability provides arbitrary write capability for 4 bytes (similar to what Copy Fail allowed). Although it is present on most Linux distributions, it requires a strict condition: the attacker must have the privileges needed to create a namespace. The problem for the attacker is that on environments like Ubuntu, namespace creation by unprivileged users is sometimes blocked by AppArmor security policies, making the xfrm-ESP attack impossible.
- The RxRPC vector: this is where the second flaw comes into play. Unlike xfrm-ESP, an attack via RxRPC does not require any privilege related to namespace creation. However, it also has a drawback: the
rxrpc.kokernel module is not included in the vast majority of distributions. That said, there is an exception with Ubuntu, since it loads this module by default!
By combining these two techniques, the exploit adapts to its environment. If the distribution allows namespaces but does not include RxRPC, xfrm-ESP does the job. If the distribution blocks namespaces with AppArmor but loads RxRPC by default (like Ubuntu), the second method takes over. As you can see, either one may be enough, but Dirty Frag combines both.
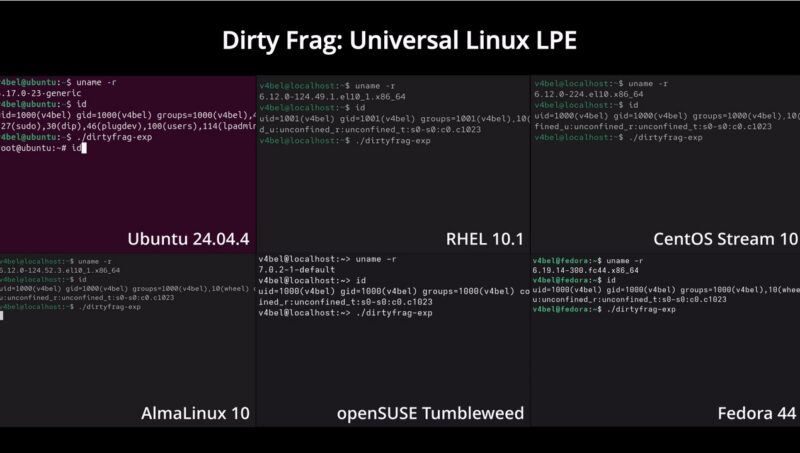
According to the information published by the researcher, Dirty Frag makes it possible to obtain root access on most Linux distributions. Want names? Here they are: Ubuntu 24.04.4, RHEL 10.1, CentOS Stream 10, Fedora 44, AlmaLinux 44, and even openSUSE Tumbleweed. A quick search on the web also shows that Debian is affected as well.
The PoC exploit code is available on GitHub and comes as a C file (exp.c).
How can you protect yourself against Dirty Frag?
From now on, everyone is waiting for one thing: official patches for all Linux distributions affected by Dirty Frag. Since the vulnerability works on a machine running an up-to-date kernel (7.0.4), a fix is expected in Linux kernel version 7.0.5. But that will not be enough, because just like with CopyFail, previous versions will also need to be covered.
In the meantime, what should you do?
Researcher Kim proposes a temporary solution. "Since the responsible disclosure timeline and the embargo were not respected, no fix is available for any distribution. Use the following command to remove the modules affected by these vulnerabilities," he explains.
Here is the command in question:
sh -c "printf 'install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n' > /etc/modprobe.d/dirtyfrag.conf; rmmod esp4 esp6 rxrpc 2>/dev/null; true"In reality, the modules are not removed. This command disables them, or blocks them if you prefer, when the Dirty Frag exploit tries to use them. It creates the /etc/modprobe.d/dirtyfrag.conf file containing the following three lines:
install esp4 /bin/falseinstall esp6 /bin/falseinstall rxrpc /bin/false
Be careful, though: disabling these modules may have unwanted side effects depending on the services running on your server. On that topic, I must admit I do not have much information (if you have any feedback, I would be happy to hear it). I saw a post mentioning a potential impact on IPSEC.
Finally, note that work is underway to patch this vulnerability as quickly as possible. For example, an article published on the AlmaLinux blog indicates that fixes are ready for testing.









