Exchange Server CVE-2026-42897: Zero-Day Flaw Already Being Exploited
A new security bulletin published by Microsoft highlights a security flaw in Exchange Server. Important note: this vulnerability, tracked as CVE-2026-42897, is already being exploited. What are the risks? How can you protect yourself? Here’s what you need to know.
CVE-2026-42897 flaw exploited in the wild
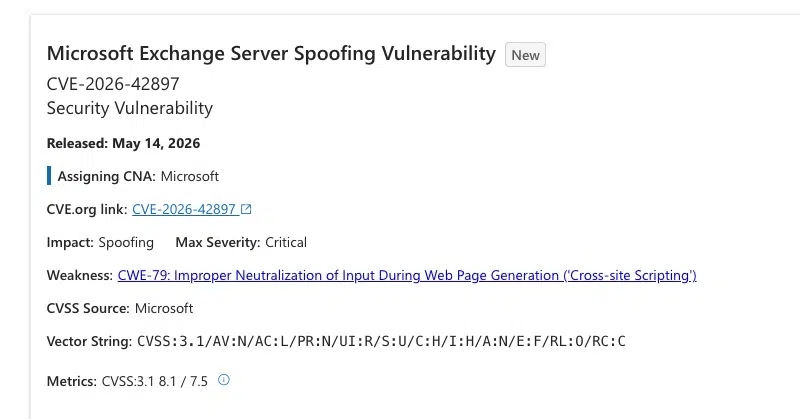
Microsoft Exchange mail servers are affected by a new vulnerability: CVE-2026-42897, with a CVSS severity score of 8.1 out of 10. It is characterized by spoofing stemming from an XSS (Cross-Site Scripting) vulnerability.
According to the security advisory published by the Redmond company on Thursday, May 14, 2026: "Improper neutralization of input during web page generation ('cross-site scripting') in Microsoft Exchange Server allows an unauthorized attacker to perform spoofing over a network."
Microsoft also provides more details on how this vulnerability can be exploited, which also involves a degree of social engineering. In fact, a cybercriminal can exploit this vulnerability by sending a malicious email to the target. If the victim opens this message in Outlook webmail, arbitrary JavaScript code can then be executed directly in the user's web browser context.
"An attacker could exploit this flaw by sending a specially crafted email to a user. If the user opens this email in Outlook Web Access and certain interaction conditions are met, arbitrary JavaScript code can be executed in the browser.", Microsoft explains.
The particularity of this vulnerability is that, according to Microsoft, it is already being exploited. However, no further details have been provided on this matter.
Affected systems and mitigation measures
It is important to note that the Exchange Online cloud service is not affected by this vulnerability. On the other hand, the following on-premises versions are vulnerable, regardless of their update level:
- Exchange Server 2016
- Exchange Server 2019
- Exchange Server Subscription Edition (SE)
In other words, there is not yet an official patch available to install. While waiting for its future release, Microsoft is offering a temporary mitigation through its Exchange Emergency Mitigation Service. This involves protecting the server by creating a specific URL rewrite rule.
How can you benefit from this protection? If you are wondering, know that it should be transparent, since this protection mechanism is enabled by default. Nevertheless, it may be useful to check the service status using the ExchangeHealthChecker script.
If you are unable to use this service, there is an alternative. This Plan B proposed by Microsoft consists of performing the following actions:
1 - Download the latest version of the Exchange on-premises Mitigation Tool (EOMT).
2 - Run the remediation script from an EMS (Exchange Management Shell) terminal.
If there is only one server to patch, run this:
.\EOMT.ps1 -CVE "CVE-2026-42897"If there are several, use this syntax instead:
Get-ExchangeServer | Where-Object { $_.ServerRole -ne "Edge" } | .\EOMT.ps1 -CVE "CVE-2026-42897"This is an official method proposed by Microsoft in this article. By the way, this article mentions a display bug: the mitigation description field may sometimes incorrectly show the message "Mitigation invalid for this exchange version". But this is only a display issue: "This issue is cosmetic and the mitigation applies successfully if the displayed status is 'Applied'. We are investigating how to resolve this issue." - The solution to this security issue itself contains an issue.