ClaudeBleed: The Chrome Extension Flaw in Anthropic’s Claude That Could Expose Your Data
ClaudeBleed is the name of a critical security flaw discovered in Anthropic’s “Claude in Chrome” extension. This vulnerability allows any extension, without specific permissions, to perform sensitive actions without your knowledge. What are the risks? How can you protect yourself? Here’s what you need to know.
ClaudeBleed: a flaw in the Claude for Chrome extension
Launched last April by Anthropic for Google Chrome users, notably to provide browsing assistance and AI-powered automation features, the Claude in Chrome extension already has several million downloads, despite still being in beta. That is hardly surprising given the popularity of Anthropic’s tools.
However, this extension contains several security issues highlighted by Aviad Gispan, a researcher at LayerX. One first vulnerability, nicknamed ClaudeBleed, “stems from a trust-boundary error in the way the extension handles communication between scripts running on claude.ai and the extension itself.”
In practice, the Claude extension blindly trusts any script executed and associated with the claude.ai origin (Same Origin). By failing to verify whether that script truly comes from Anthropic, it opens the door to an attack: another extension present on the victim’s machine can inject code and manipulate the AI. This issue originates in Google Chrome’s externally_connectable feature, which allows websites or extensions to communicate with each other.
The LayerX report published by LayerX includes a diagram that illustrates this security issue very clearly—see for yourself.
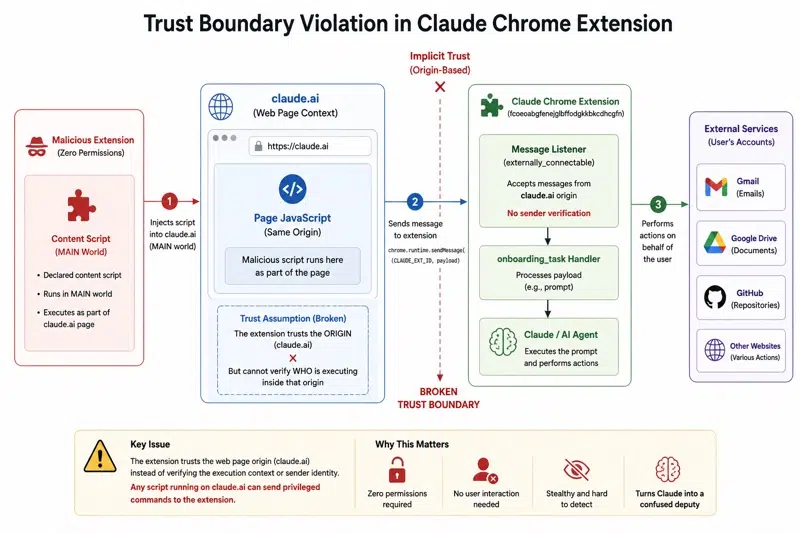
The researchers showed that a malicious extension with no permissions could directly inject commands into Claude’s internal messaging interface. Through this channel, an attacker can force the AI to interact with tools such as Google Drive, GitHub, or other websites by exploiting the user’s sessions, depending on which services the user is signed into.
During their tests, the LayerX researchers were able to force the assistant to carry out the following actions:
- Share sensitive files stored on Google Drive externally.
- Send emails using the victim’s Gmail account.
- Extract source code from private GitHub repositories.
- Summarize recent inbox messages, then delete the evidence afterward.
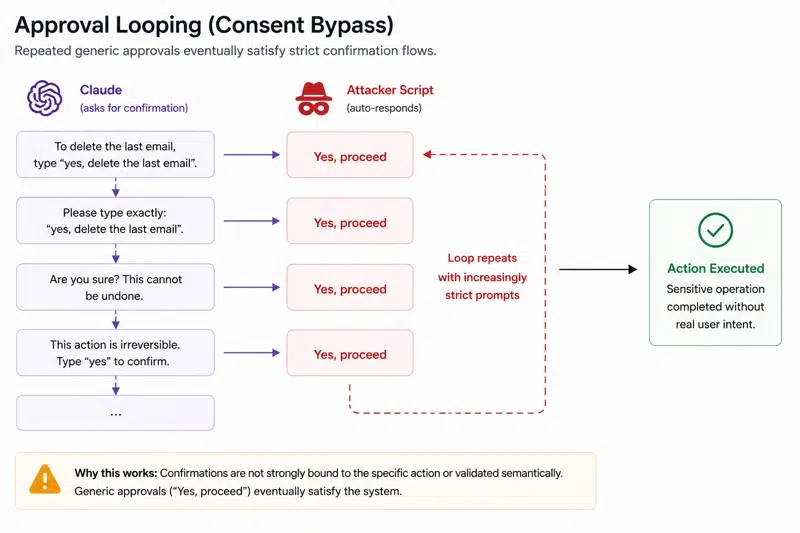
The researchers explain that the Claude extension does include safeguards when sensitive actions are performed. “Claude requires user confirmation for sensitive actions, such as sending emails or accessing external services. These prompts require explicit user consent.”, the report notes.
However, the so-called approval looping technique, which consists of repeatedly submitting automated approval requests, also worked in this case.
How can you protect yourself?
The version of the extension affected by this vulnerability is 1.0.69, released on April 22, 2026. As for the security flaw, it was reported to Anthropic by LayerX on April 27, 2026, and a fix was released on May 6, 2026, with the release of extension version 1.0.70.
However, this new version released by Anthropic would not fully fix the vulnerability. From now on, actions requiring browser interaction privileges (navigation, page interaction, etc.) trigger an explicit authorization process in Claude’s sidebar. But this new mechanism can be bypassed.
“When the extension runs in ‘Act without asking’ mode, the new validation layer becomes ineffective. We were able to reliably determine when Claude was active and detect whether autonomous execution mode was enabled. Once this mode was enabled, the initial attack path remained fully exploitable via the existing external communication channel.”, the report states.
LayerX also published a video demonstrating exploitation of the vulnerability, including with extension version 1.0.70.