Researcher Proves Microsoft Edge Can Leak Passwords Into Memory
EdgeSavedPasswordsDumper is the name of a tool designed to highlight a security issue in Microsoft Edge: the browser reportedly stores passwords in clear text directly in the memory of its process. Microsoft knows about it.
Passwords Exposed in Plain Text in Edge Memory
Tom Jøran Sønstebyseter Rønning, a security researcher, has uncovered something that is bound to raise eyebrows. Then again, why would anyone store their passwords in a web browser, right? There are so many better things to do with a proper password manager.
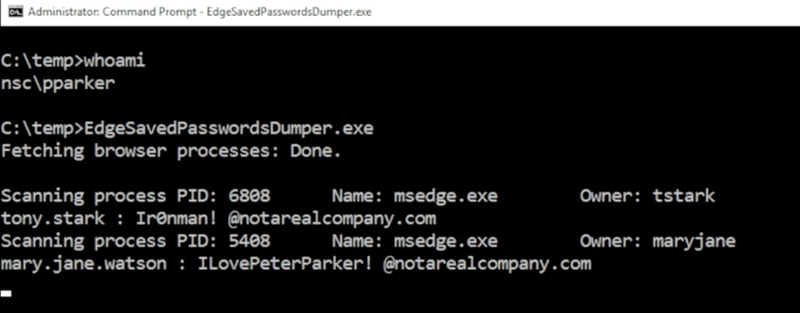
Back to the story. This security researcher created a tool called EdgeSavedPasswordsDumper. Available on GitHub, this PoC highlights how credentials saved through Microsoft Edge's autofill system and password manager are loaded in clear text into the browser's parent process.
According to him, all credentials are loaded in clear text into memory. Even if you have not used a specific credential, it is already preloaded into memory by Microsoft Edge. On X, Rønning claims: "Microsoft Edge loads all your saved passwords into memory in plain text — even when you are not using them."
Since Microsoft Edge is based on Chromium, you might think that other Chromium-based browsers are affected too. I'm thinking of Google Chrome, of course, but also Brave. In reality, no. This vulnerability is specific to Microsoft Edge and likely tied to its close integration with Microsoft's built-in password manager.
When a web browser is running, it typically launches a main process and a set of child processes, notably for the different tabs. In the case of credentials, the child processes spawned by Edge do not contain the credentials; the parent process consistently keeps this sensitive data.
This means a malicious actor with sufficient privileges can extract this data using native tools. Rønning explains that simply using Windows Task Manager is enough to perform a memory dump and recover usernames and passwords.
According to the tests carried out by the researcher, this security issue is still present in version 147.0.3912.98 of Edge. At the time of writing, this is the latest version, as it was released on April 30, 2026.
By Design: Microsoft Owns It
According to the researcher, the Redmond-based company reportedly described this behavior as "by design". This suggests two things:
- No patch will be released to fix this vulnerability,
- Microsoft knows that its web browser works this way to handle credentials.
However, the data is not stored in clear text. On your PC's disk, the credentials are encrypted with AES, and the decryption key is protected with Windows' DPAPI (Data Protection API) component. But as you may have understood, once you launch Edge, the passwords are exposed in plain text: they are decrypted and loaded into memory.









